Tooting My Own Horn
Just for the record, I get a lot of predictions wrong, but here's one I got right (at least long term) back before the iPad launched:
But, let's offer a wildcard alternative: fully wireless sync with your current Mac ecosystem. Perhaps this would be extended to some iPhones and iPod touches too ”” say just the 3GS. I expect Apple to play up sync in general in the future. As iTunes goes, so goes Apple's overall strategy. The introduction of “Home Sync” quietly last year is something I believe will be the harbinger of bigger plans, with Apple returning to sync in a big way this year after pretty much letting its previous strides rust and be forgotten (think of the big push on sync services in Mac OS X Tiger back in 2005 and those features integration with the service then known as .Mac and now christened MobileMe).
Clearly, iCloud is for Apple this decade what iTunes was for Apple last decade.
Outlawed By the Cloud
John Gruber linked to a story from Martin Kekkelund in which he tells of a friend whose Kindle was wiped and her Amazon account terminated for some alleged affiliation with another account. But, she didn't know what other account Amazon was referring to or what violation the company could have in mind — and Amazon refuses to tell her. Outrageously, she has lost her Kindle library of books and has basically no recourse:
Linn lives in Norway, far away from Amazon's jurisdiction. How will she ever find the means to get her books back? By suing a large corporation half-way round the earth?
Linn is outlawed by Amazon.
I might wonder if this is a legitimate story, save for that I have a similar one with Google. For years I ran several web sites, including Open for Business, which depended on Google AdSense for ad revenue. Google offers good rates for advertising and I liked using text based ads over the flashing garbage many ad networks put out.
It worked fine until Google decided I had violated some term of their agreement concerning the displaying of ads. But, they wouldn't tell me what I had allegedly done nor would they allow me to prove my innocence (I reviewed the terms and had violated none of them). Much as in Kekkelund's friend's case, I only received maddening replies from the company. They even refused to pay the last bit of ad revenue they owed me.
Also, as in the story I linked to, the impact was profound. It is very hard for a little web publisher to find a good quality, reputable advertising network that can generate even enough revenue to pay for site maintenance these days. Google has dominated the field for some time now with what is effectively a monopoly in actually profitable advertising, so that when Google permanently bans you from their system without any sort of corporate equivalent of “due process,” the result is crushing.
Why would Google ban my small business from its systems? Why would Kekkelund's friend receive such an unhelpful response from Amazon? In each case — and I would wager, many more — there is no good answer and that is frightening.
For many people and businesses, much of one's livelihood is tied up in just one or two cloud providers. I think the question we need to ask is this: “if any one provider shut down my account, would I be shut down?” If the answer is yes, you are too dependent on that provider.
My conversation with Google is below the fold.
Fonts
Results showed male subjects had an easier time recognizing Frutiger and thus spent less time glancing at the display and more time focused on the road ahead. Average glance time with Frutiger was 10.6 percent lower for men, and while that may sound insignificant, researchers say it works out to about 50 feet when traveling at typical highway speeds.
And people pretend that fonts don't matter.
Jeff Bezos is the New Steve Jobs
Gruber writes:
Om Malik argues that Bezos is the inheritor to Steve Jobs's crown. I agree. Not because Bezos has copied anything Jobs did, but because he has not. What he's done that is Jobs-like is doggedly pursue, year after year, iteration after iteration, a vision unlike that of any other company ”” all in the name of making customers happy.
The jury is still out on whether the new Kindle Fires can be the first real competitor to the iPad. But, Amazon already has the only alternative vision to Apple's that is compelling on its own right. The expansion of Prime makes it easier and more enjoyable simply to go to Amazon for everything. If Amazon can get the Kindle Fire software to be mature enough to stand up to iOS, I wouldn't want to have to compete with Amazon.
HP Introduces the New iMac
A brilliant headline for an on spot article. To be sure, it isn't an exact clone, but to the average consumer, it would be easy enough to confuse the new HP Spectre One with an iMac — it has many design cues that originated with the Apple iMac. Most blatant of all are the keyboard and trackpad, which are inexcusable knockoffs of the Apple Keyboard and Magic Trackpad. I'm sure many of the same people who defend Samsung for its most dubious acts of iOS cloning will defend HP too, but I don't really see how anyone wins when some of the biggest technology companies spend more time trying to create fake Apple products than they do innovating.
What if HP had kept producing its innovative WebOS product line instead?
HT: Gruber
Navsop
An intriguing developing technology:
Unlike GPS, Navsop doesn't need satellites once it's got going, so it doesn't rely on a signal coming from the sky. That means it can be used indoors and even underground, both places that GPS can't go because the signals are too weak, having journeyed all the way from space. By contrast, radio, TV and mobile signals are much stronger.
Most cell phones already use EGPS, which works in a similar way, but this sounds like a significant expansion of that concept.
Hybrid Devices
Bill Gates “speaks on”: Microsoft Surface and the “other” tablets:
“I actually believe you can have the best of both worlds. You can have a rich ecosystem of manufacturers and you can have a few signature devices that show off, you know, wow, what's the difference between a tablet and a PC.”
As nice as the idea is in theory, so long as Metro and Classic Windows are almost like two different systems that can run parallel on the same system, I don't think Microsoft has found the “best” of any world. Whether having a traditional Windows “experience” next to the tablet interface is something people will want will be telling when Windows 8 comes out.
Impact
It is hard to believe that the iPhone landed five years ago today. I remember heading out to observe the launch day festivities and trying an iPhone for the first time — it felt like using something out of Star Trek. However, as nifty as it was even at a demo kiosk, the iPhone was significantly different from anything before it, and so it was hard to figure out precisely how useful it would actually prove to be. I wrote about my buyer's indecision after I succumbed to the temptation to buy one.
While very little about the iPhone was “innovative” when the first generation model's features were placed in isolation, putting them all together into a very thin, capacitive touch screen-only device was strikingly innovative. Often times, these are the best sorts of innovations: ones that take a pile of good ideas that are sitting scattered around and putting them together into something new that has a cohesive vision. Before the iPhone, smartphones weren't terribly easy to use and presented users with a very strong step backwards in usability from the mouse driven interface of a desktop computer. With the iPhone, suddenly common tasks such as web browsing were as easy, if not easier, to do on a phone than on the computer.
That's why the iPhone made such a big impact. It is also why these stock growth statistics look as they do.
My Desktop from Ten Years Ago
I ran across this screenshot today and thought it was interesting. This is what my desktop on my computer looked like ten years ago.
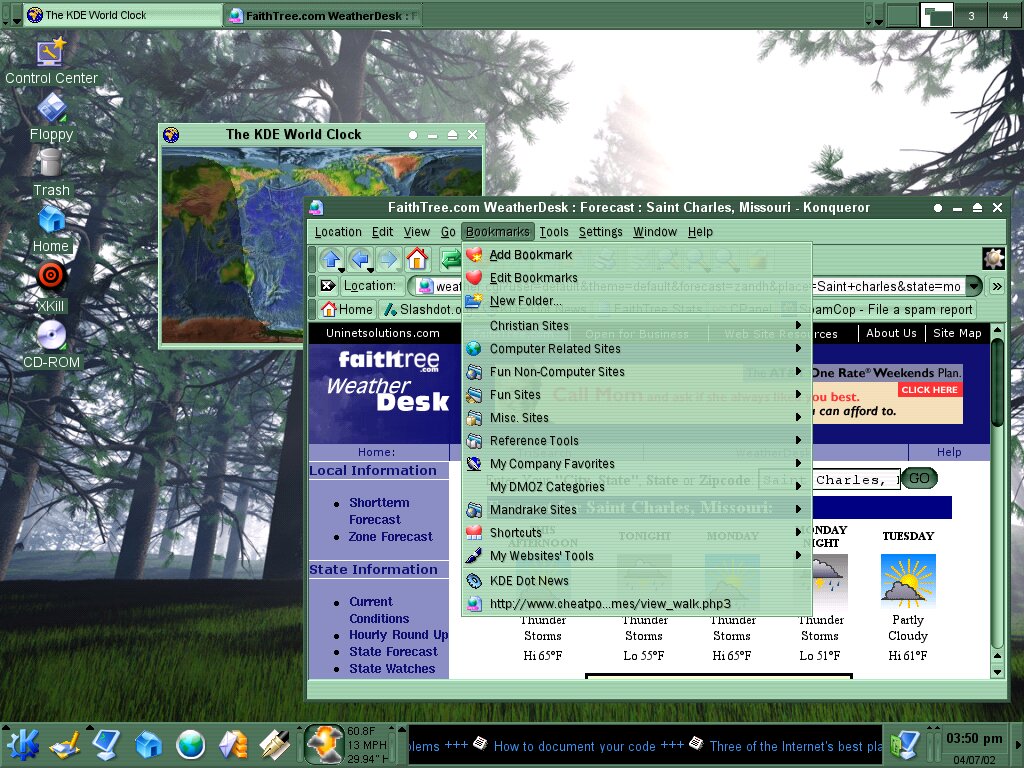
Interfaces have definitely improved since then.
Microkia
Gruber quoth:
If I'm right, it's inevitable now that Microsoft will acquire Nokia.
I think he is right. It doesn't really make sense for Microsoft to target the tablet space with its own, tightly controlled product line and ignore the cell phone market. The two markets clearly feed off each other and, assuming the Surface does well, it will do well in stark contrast to the dismal sales record of Windows Phone 7. While the Zune fiasco shows that Microsoft can fail with hardware, the Xbox 360 is a good argument that Microsoft can also do quite well with its own hardware. Acquiring a company that is acting idiotically, but yet also brings major cell phone design talent with it, would be a good choice if Microsoft wants to make a massive first party splash into the mobile world.






